Introduction: Unveiling How Non-VBV Cards Bypass 3DS Protocol – Easy way possible
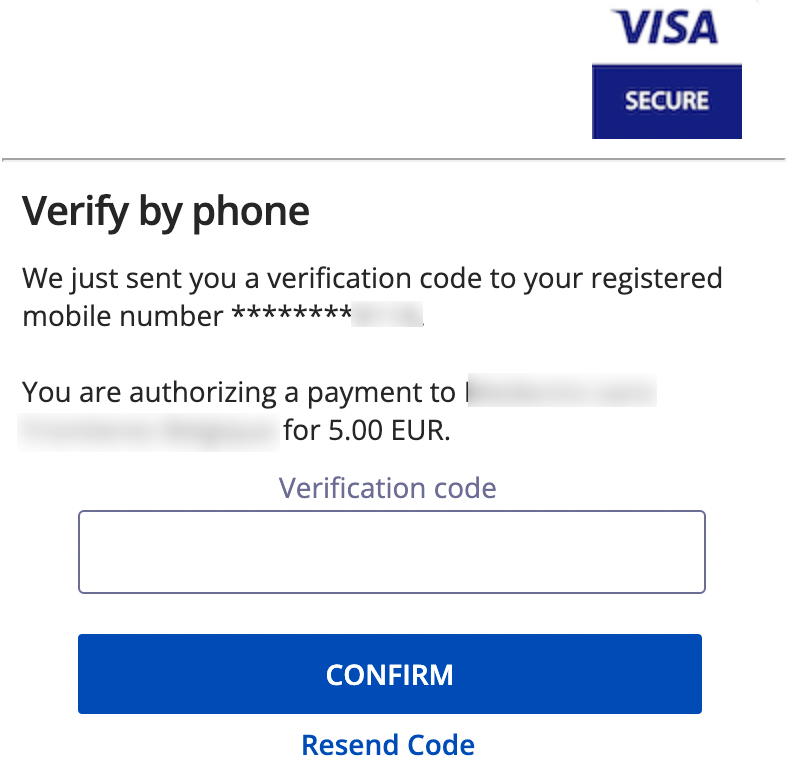
Utilising 3DS, VBV, and MSC security standards has made it exceedingly hard for individuals all around the globe to use fraudulent cards. A few years ago, banks and payment processors introduced this additional level of protection to internet transactions. It adds another stage to the verification process. This generally means inputting a unique code that was received by SMS or email to prove the buyer’s identity. How Non-VBV Cards Bypass 3DS Protocol.
The 3D Secure Protocol:
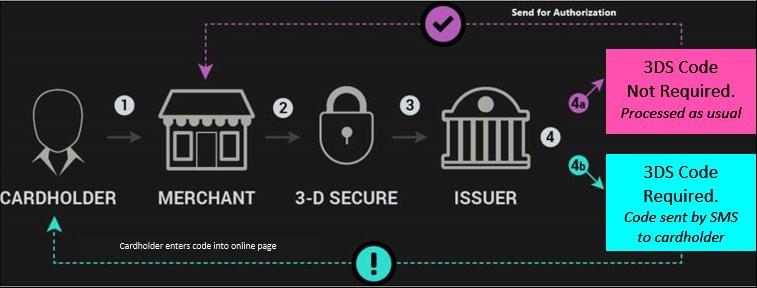
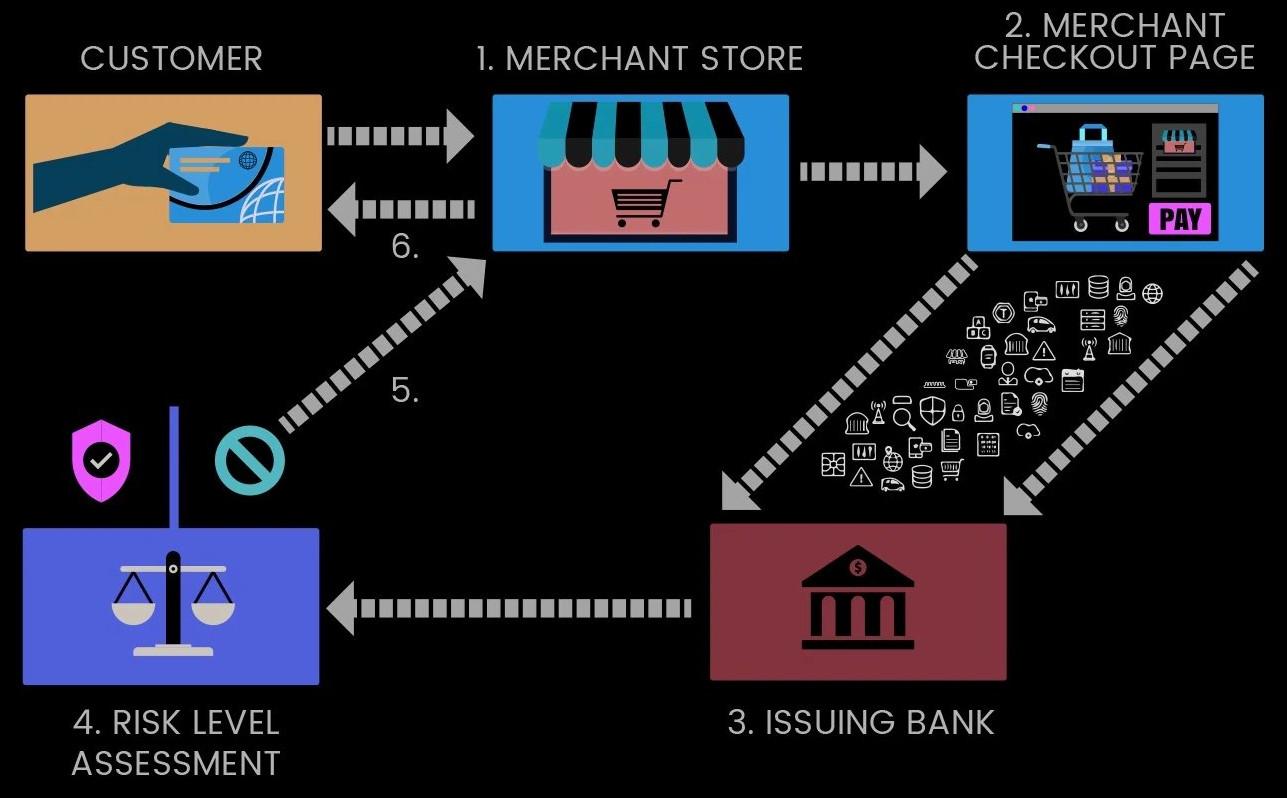
To appreciate the current demand for non-VBV cards, one must first comprehend the function of 3D Secure (3DS) and its impact on digital commerce. Ten years ago, developers designed this protocol to combat fraudulent online transactions. It operates through a tripartite framework: the merchant and their acquiring bank, the cardholder’s issuing bank, and intermediary payment networks such as Visa and MasterCard. How Non-VBV Cards Bypass 3DS Protocol
In the nascent stages of e-commerce, fraudulent activity posed a severe threat. A surge in contested transactions resulted in substantial financial losses for both banks and retailers. The 3DS system provided a resolution by introducing an additional identity verification step—commonly involving a one-time password or biometric confirmation—before authorising payments.
Merchants favoured this system, as it absolved them of liability for fraudulent transactions. Under 3DS, responsibility for unauthorised purchases is shifted to the issuing bank rather than the vendor. Consequently, the adoption of 3DS became advantageous for retailers, safeguarding them against financial losses arising from fraudulent activity.
Not all online retailers employ 3DS verification. Certain merchants, particularly those operating in highly competitive sectors, are cautious about introducing additional authentication steps that may deter potential customers. They recognise that excessive security measures can dissuade buyers, leading to abandoned transactions—a significant concern for businesses prioritising sales volumes.
Some vendors have determined that accepting marginal losses due to fraud is preferable to sacrificing revenue from incomplete purchases. Consequently, they forgo 3DS, particularly for low-value transactions or in fiercely contested markets. This represents a deliberate compromise between security and transactional convenience.
2D Sites:
Given the inconsistent adoption of 3DS, online retailers now fall into two distinct categories. The first consists of merchants with robust 3DS protection, where fraudulent activity is substantially more difficult. Such secured platforms are becoming increasingly prevalent as retailers emphasise fraud prevention. Conversely, unprotected sites—commonly referred to as “2D merchants”—remain vulnerable to exploitation.
The pool of 2D merchants, being more susceptible to fraudulent transactions, is gradually diminishing. This shift has precipitated heightened demand for non-VBV cards among carders. With fewer unprotected targets available, fraudsters increasingly seek non-VBV cards to sustain their operations. How Non-VBV Cards Bypass 3DS Protocol
Comprehending this dynamic is essential for those engaged in fraudulent activities. Non-VBV cards hold considerable value not merely due to their scarcity, but because they circumvent 3DS authentication. As more retailers adopt stringent security protocols, opportunities to exploit standard cards diminish—rendering non-VBV cards even more desirable and costly. How Non-VBV Cards Bypass 3DS Protocol
Enhanced Transaction Security “3DS 2.0”:
The introduction of 3DS 2.0 has significantly altered the landscape of online transactions. This advanced iteration surpasses its predecessor by employing dynamic risk assessment to determine when additional authentication is necessary. Consequently, even VBV cards may occasionally bypass the 3DS prompt, depending on contextual factors. How Non-VBV Cards Bypass 3DS Protocol
3DS 2.0 evaluates each transaction in real time, analysing variables such as purchase value, merchant reputation, and the cardholder’s typical spending patterns. Based on this assessment, the system either requests supplementary verification—such as a one-time passcode—or permits the transaction to proceed unimpeded.
From a merchant’s perspective, 3DS 2.0 offers substantial advantages. It strikes an optimal balance between security and user convenience, potentially reducing cart abandonment rates while maintaining robust fraud prevention. Retailers benefit from enhanced protection without invariably subjecting customers to intrusive authentication steps.
However, for carders, this inconsistency proves problematic. The inability to reliably bypass 3DS introduces operational uncertainty, as previously functional cards may unexpectedly demand authentication—increasing the risk of detection.
This volatility underscores the heightened value of non-VBV cards. In an era dominated by 3DS 2.0, possessing cards that consistently evade authentication is indispensable. Such assets represent the most viable means of achieving predictable outcomes across diverse merchant platforms. How Non-VBV Cards Bypass 3DS Protocol
Non-VBV BINs and Cards:
Non-VBV BINs have become increasingly scarce and consequently command a premium value. The carding community highly values these BINs and associated cards, which fall into two distinct classifications:
1. Selectively exempted cards:
These are issued by banks that have implemented 3DS but have configured specific BINs to bypass additional authentication. This exemption may apply to high-net-worth clients who prioritise transactional convenience or are part of a risk-based authentication system where lower-risk transactions proceed without secondary verification. How Non-VBV Cards Bypass 3DS Protocol
2. Non-Compliant issuers:
These originate from financial institutions that have not adopted 3DS protocols. While increasingly uncommon, certain smaller banks or regional entities may still lack 3DS implementation due to cost constraints or operational considerations.
From a merchant’s perspective, both categories function identically. When using a 3DS-enabled platform, transactions with either type of non-VBV card go through without extra authentication, which is important because it lets them be used on many websites, even those that have 3DS protections. How Non-VBV Cards Bypass 3DS Protocol
It is worth noting that only a minority of 3DS-compliant merchants actively reject non-3DS cards. Most platforms are configured to authorise such transactions, prioritising sales conversion over the security advantages of full 3DS verification.
For fraudsters, cards that circumvent VBV prompts are particularly advantageous. These transactions are recorded as “3DS authenticated” within merchant systems despite bypassing verification, rendering them indistinguishable from legitimate purchases—thereby maximising transactional integrity from the carder’s perspective.
Shop link to buy Carding tools
Visit Dumpseller Shop Now to see our newly in store Carding products, Bank Transfer, Cashapp Transfer, Venmo Transfer, Dumps with pins, Bank logs, CC Linkables and many more.